Atlanta, GA – September 3, 2018 – Supply chain attacks, in which an enterprise shares information with a third-party vendor and that vendor gets hacked, are on the rise. According a recent report, 90 percent of those surveyed confirmed experiencing a software supply chain attack, with the average cost of an attack at over $1.1 million.
Weak links between the two parties involved in the transaction can be easily exploited by hackers, creating a domino effect between the vendor and  enterprises, says Trevor Horwitz, CEO and co-founder of iTrust.
enterprises, says Trevor Horwitz, CEO and co-founder of iTrust.
“The other way that a cyber supply chain attack can occur is where there’s actual direct connection between a vendor and the enterprise,” says Horwitz. “They can connect their systems and when that vendor gets compromised, the hackers can get into the systems themselves.”
“Target is probably the most prominent example since they got hacked through their heating and air conditioning vendor. It ended up causing $250-plus million worth of damage to their business.”
Horwitz shares that, in his two decades of cybersecurity work, he realized that many of his clients had very little insight into their third-party-related cybersecurity risk.
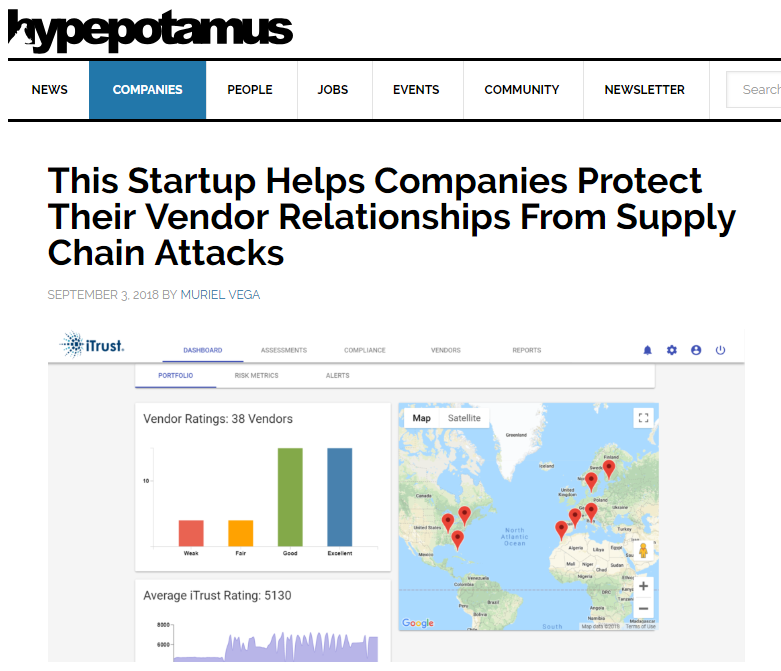
Founded in 2016, iTrust provides more information for enterprises entering into potentially-risky relationships with vendors. The platform generates cybersecurity risk ratings and intelligence so decision makers can be more aware.
“There’s risk ratings to determine whether or not they want to do business with that vendor and enter into a trust relationship,” says Horwitz. “Then, on an ongoing basis, we continue to do assessments to ensure that the vendor is complying with cybersecurity best practices and also maintains compliance against regulatory standards.”

iTrust’s platform monitors vendor compliance status and expiration dates with regulations like HIPAA, PCI and more, collects reputation ratings from those in the industry, monitors vulnerabilities in the network and web application security. It works as the bouncer between the enterprise’s sensitive data and the vendor.
The product is fully automated once the iTrust team onboard a client, says Horwitz. “The last thing we want to do is to provide another tool that would be labor intensive for enterprises, because everyone in cybersecurity already doesn’t have enough resources to fulfill the current mandates.”
“Our platform is all based on trust and that means that we won’t do any evaluation or scan of their vendors and resources for a risk rating unless the vendors opt into the platform. There’s very little pushback from them because they trust us.”
Enterprises can enroll on the platform on subscription basis for a fee based on how many vendors they’re monitoring. iTrust’s main clients are healthcare and service providers, with financial services as their biggest industry.

The team has recently been accepted in the Queen City Fintech Accelerator in Charlotte, NC, though upon first glance, they are a bit different than most of the startups that go through the program. iTrust is already in scale-up mode, shares Horwitz. They will be using their time at the bank-backed accelerator to truly penetrate the financial services industry and get to know their potential customers.
“We have reached significant technical milestones, but now the focus is really on sales and marketing. Can we develop a bigger channel and penetrate even larger customers than we already have?”
iTrust raised a seed round in early 2017 and will ramp up fundraising for a Series A upon completion of the accelerator.